With so many supply chain partners, the reality is that you cannot trust the manufacturing process’s security to ensure that the hardware, firmware, or credentials of the device were not altered.
In a recent webinar with Kaeo Caindec, principal analyst with the Farallon Technology Group, we discussed how manufacturers could gain control of device security within their complex supply chain, all through a zero trust manufacturing approach.
You can watch our discussion today and read some of the high-level takeaways from our recent webinar on Zero Trust Manufacturing: How to Embed IoT Device Security in Your Supply Chain.
What is Zero Trust Manufacturing
Let’s start with understanding the “zero trust manufacturing” approach and how it can better secure your device manufacturing lifecycle.
With connected devices and IoT on the rise, we’ve got billions of devices that are out there. And not just home devices, but also industrial control devices that pose safety risks. When we talk about zero trust manufacturing, we’re really talking about an approach to designing and manufacturing, testing, and delivering trustworthy products.
When you think about the design process and the number of companies involved from designing it in computer-aided design (CAD), embedding chips and devices and components, all of the software developers involved throughout the process, and the challenges of delivering the product safely. At each point, there are many points of entry for someone to compromise the device.
Zero trust manufacturing is about really taking a look at the whole process end to end to make sure that we’re producing and delivering trustworthy devices.
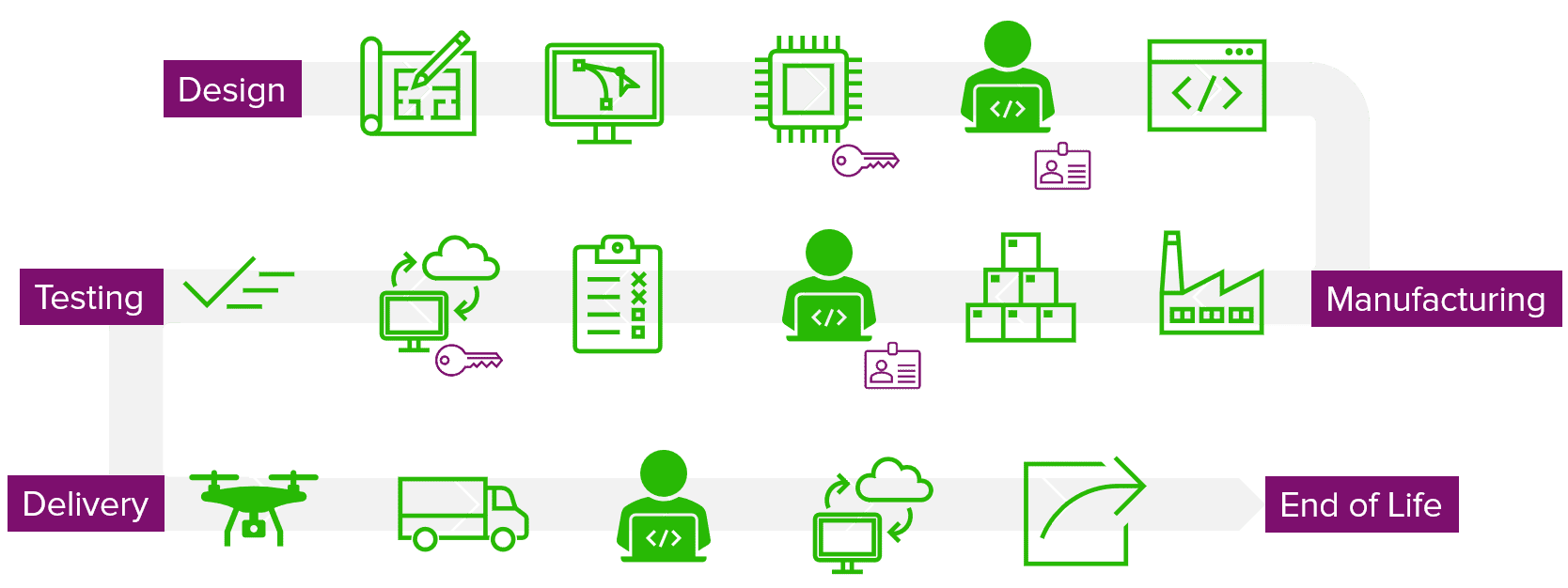
You can see in the diagram above that there are keys and there are ID cards at certain places. This delivery cycle shows the multiple steps to figure out what type of key, certificate, or credential you need to place.
Whether it’s on somewhere in a secure element, on a piece of hardware where you’re going to do a private key, or in the factory when you’re making it, you need a holistic strategy from the beginning
For example, you have to have an authorized workstation that will perform the key generation, key injection, and the key’s end of life to protect against breaches and vulnerabilities.
Typical Breaches and Vulnerabilities
These attacks, interestingly enough, follow a fundamental pattern:
- The threat actor, or the bad guy, either sends a phishing email or
- Directly attacks a system.
- They’re often doing either a reconnaissance to steal and listen for credentials or breaking into a process to steal private information about the devices themselves.
- They can use that to penetrate further and compromise a device. In this case, it could be a device within an industrial OT network. From that device, they can begin to launch lateral attacks, and this same pattern is used repeatedly for everything.
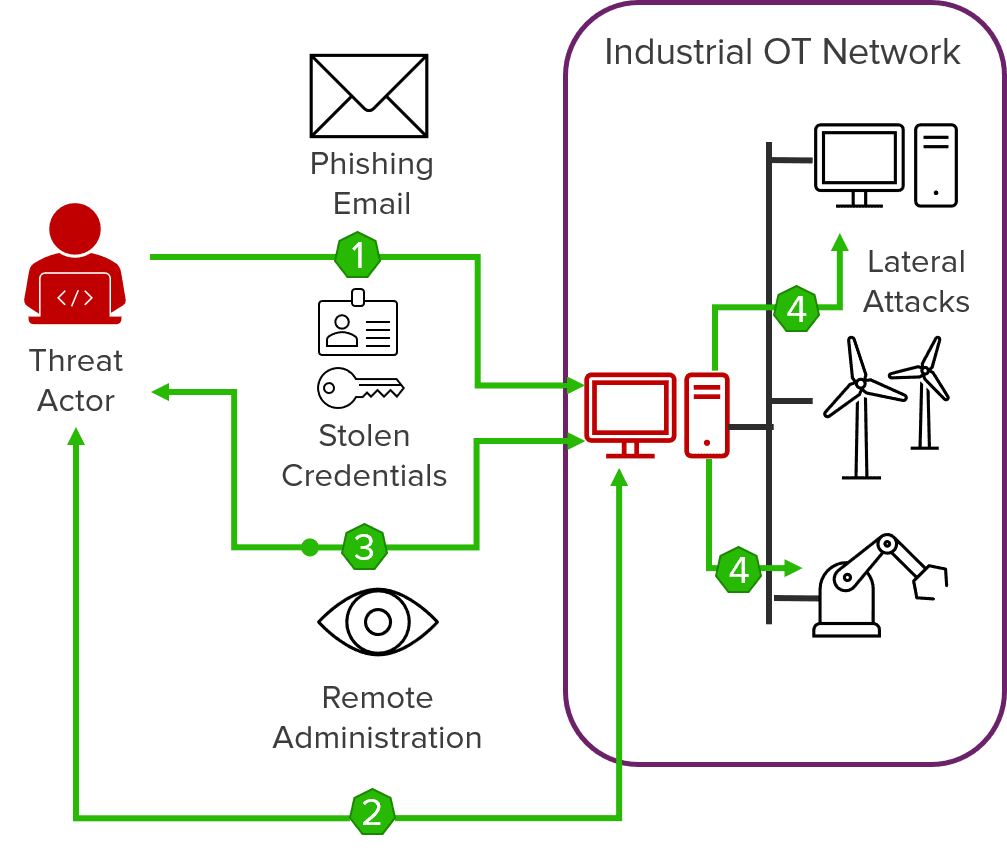
While 80% of breaches involved brute force or stolen credentials, we’re not just talking about the information here or data or privacy. We’re talking about threat actors that compromise devices to take control.
Zero Trust Manufacturing vs. Zero Trust Networking
Forrester coined the term “zero trust networking” several years ago. Zero trust networking is all about ensuring that end-users and devices can access a network securely. Fundamental tenets of deploying a zero trust networking architecture include: providing access controls that can authenticate the end-user or do two-way multi-factor authentication.
This means putting safeguards to prevent the escalation of privileges and using micro-segmentation, firewalls to access everything from private, back-end, enterprise IT systems to the public cloud, and IoT network and devices.
This approach focuses on authentication, encryption, login, user, and password-protected databases. However, this view relies on the fact that you trust the people, trust their credentials, and trust that they are who they are.
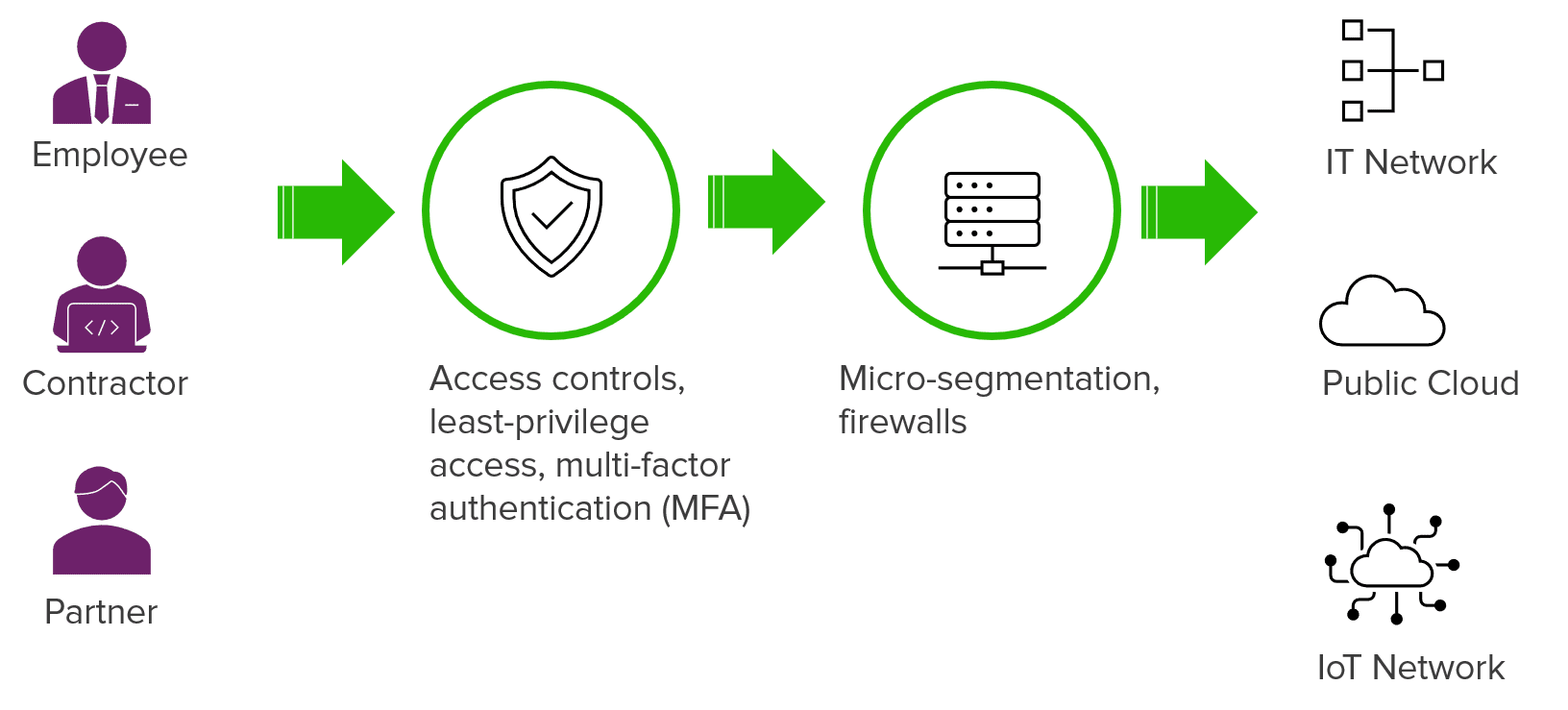
Zero trust networking can fall apart because it doesn’t define how to ensure that you can trust the devices’ credentials and identities communicating on the network.
With zero trust manufacturing, you’re ensuring the integrity and trustworthiness of the systems and the devices, while zero trust networking ensures that you’re communicating securely.
Zero Trust Manufacturing Best Practices
Ready to learn more about zero trust manufacturing? Watch the on-demand webinar to get more insights into what it takes to deploy a zero trust manufacturing approach. You’ll learn more about the supply chain complexities and challenges and how to start embedding IoT device security into your supply chain.


![[Webinar Recap] Using Zero Trust Manufacturing for Supply Chains](https://www.keyfactor.com/wp-content/uploads/What-is-Zero-Trust-Manufacturing.png)