That’s a wrap!
Thanks for the 450+ attendees that came out (virtually) to Keyfactor’s inaugural Critical Trust Summit. We covered a lot over the last two days on how your teams drive crypto-agility in your organization.
You had a chance to watch 15+ sessions, hear from 20+ speakers, network with fellow industry experts, and hopefully learn something new.
If you missed day 1, read the recap blog to get caught up.
Here are some of the highlights from day 2, and don’t forget, you can watch replays of all sessions from both days right now.
Unified Cryptography Management & Product Innovation
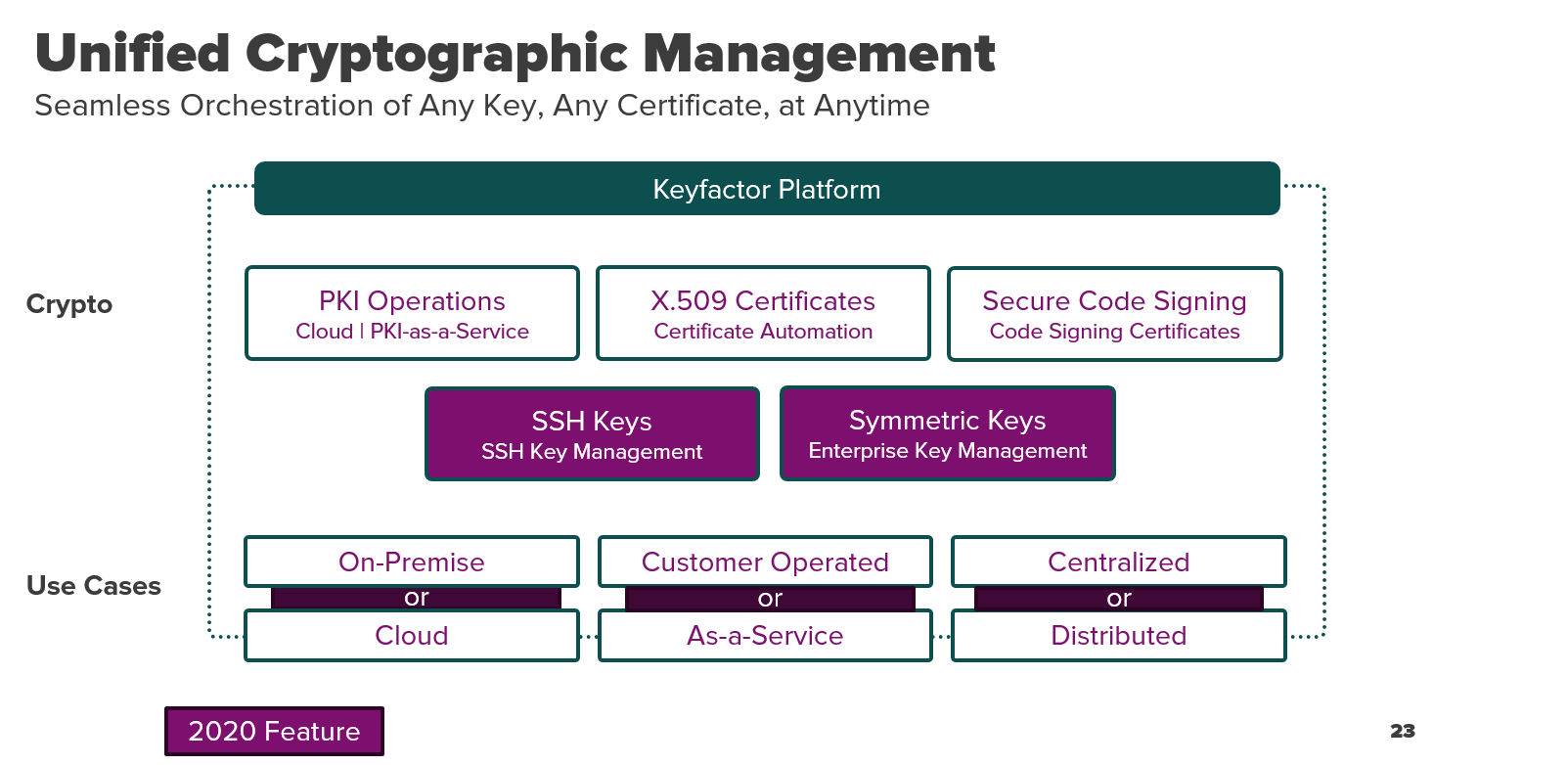
We kicked off the day with a quick coffee break and then jumped into our opening keynote on how your team should approach unified cryptography management (UCM).
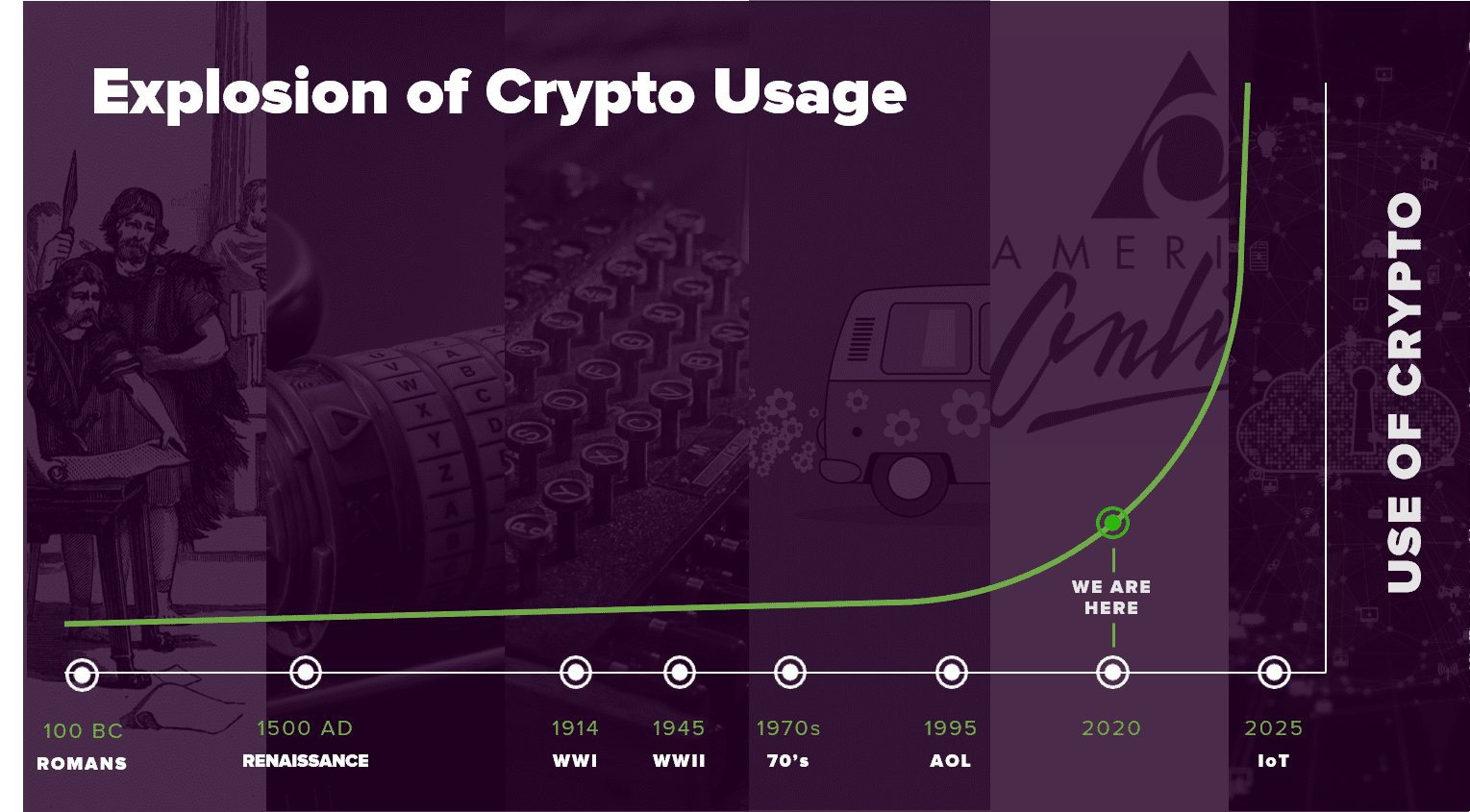
Our co-founders Kevin von Keyserling and Ted Shorter took us through the history of cryptography and how a unified approach to managing your diverse cryptography is the strategy for the future.
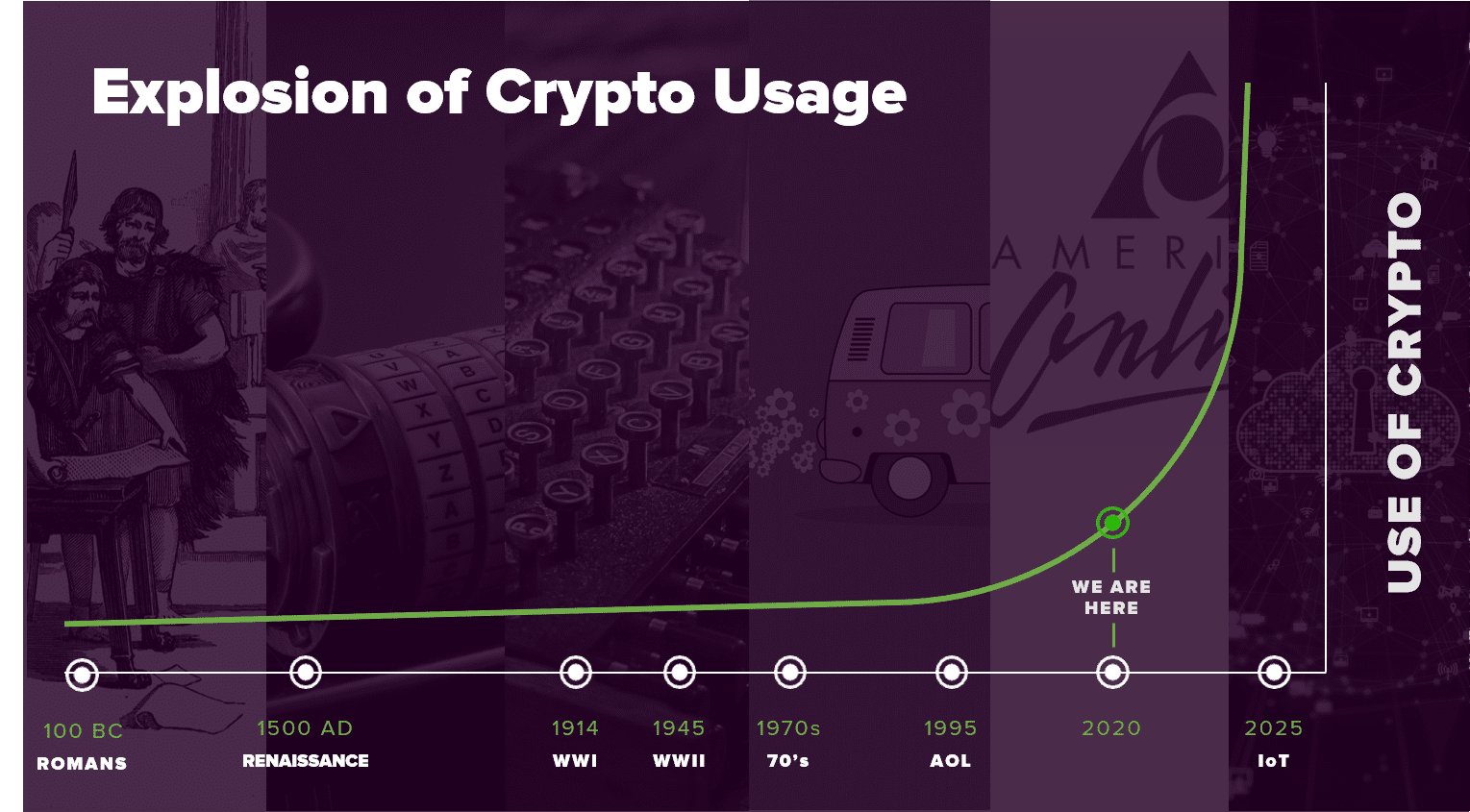
Kevin showed how Keyfactor is in a unique position to help our customers orchestrate and scale their use of cryptography for both enterprise and IoT use cases.
Every single one of your devices that’s being connected, whether it’s a tire sensor, a jet engine, a train, has to think about every single component on that device, that machine, and how they’re going to give it a digital identity with integrity.
And to do that, you need to have a software platform that’s going to have massive scale, so you can authenticate every single device, every single electronic component.
Ted shared a vision of how unified cryptographic management impacts Keyfactor’s strategy from a product perspective. According to Ted, “When we look at applying that principle to all keys, we’re really looking at this now is cryptography-as-a-service and from that perspective, you really overlay what we have inside of the platform.”
Mark Thompson and Ryan Sanders took us through a deep dive into the importance of SSH key management in their session, Protecting SSH Keys in Multi-Cloud Operations. SSH Keys are everywhere and present different management challenges than X.509 certificates.
Mark discussed some ways you can mitigate against SSH-based attacks, including:
- Disable root login
- Use public-key authentication
- Use strong passphrase for keys
- Set a custom SSH port
- Keep SSH updated
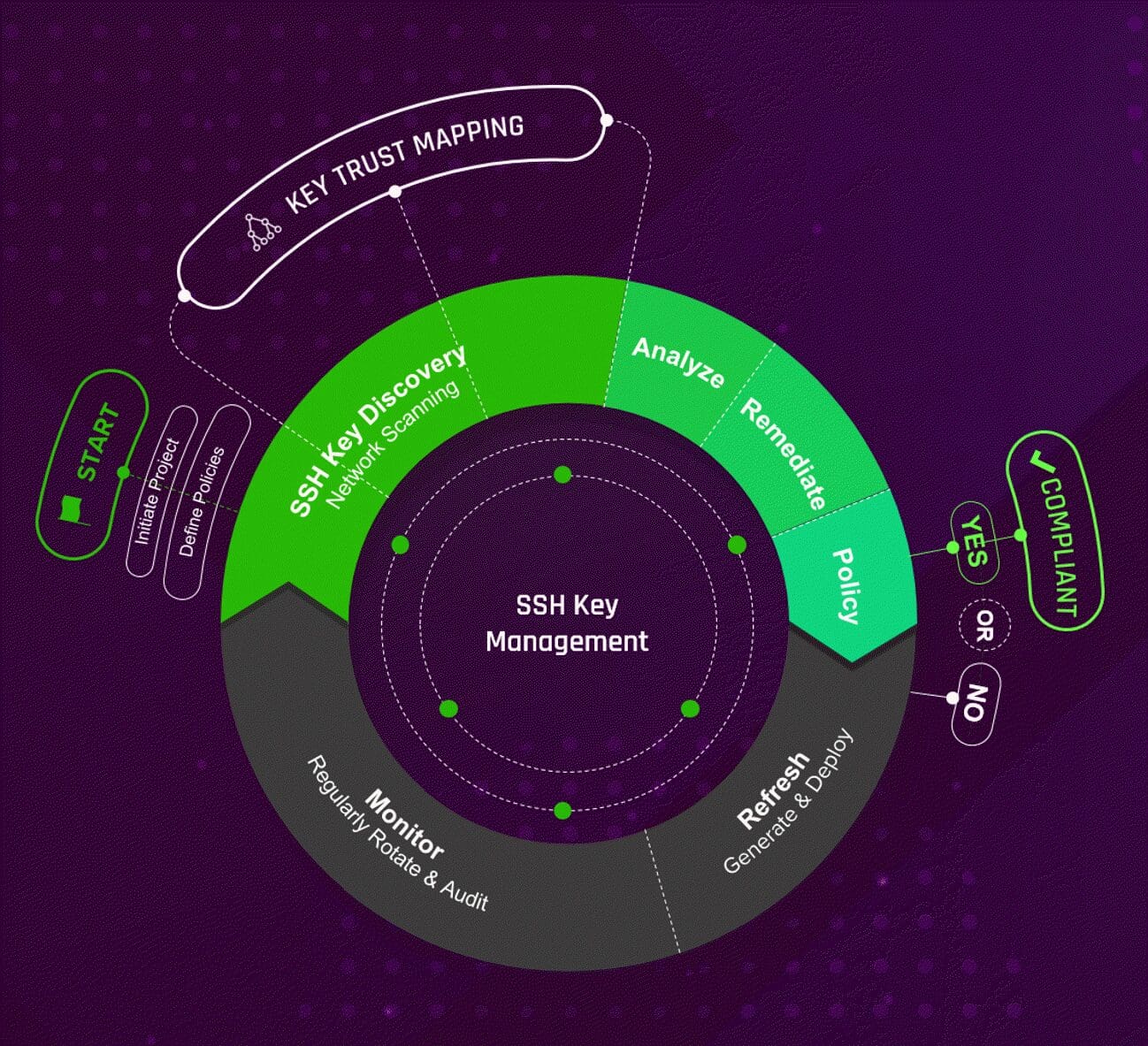
Request a demo today to see how the entire Keyfactor platform, including our new SSH key manager.
Insights from IoT and PKI Experts
It’s not every day that you get to hear from expert practitioners in cryptography management and IoT device security.
Brandon H, from Abbott, and Ken Pierce, from General Motors, talked with our director of IoT Product Management Ellen Boehm on some real-world results from IoT manufacturers.

Towards the end, Ken and Brandon both closed with some great advice for the audience.
“Never write your own cryptography and if you’re new and you want to learn, you go to the forums for your industry or something close to that so that you can learn,” said Ken. “You don’t have to give away ideas, but you’ll get the expertise you need to make some forward progress.”
“Don’t assume that just because you have certs of cryptography that your implementation is secure,” said Brandon. “There’s a lot that goes around your implementation, not just the fact that you are using certs or TLS or things of that nature. So, take a look at the periphery of how your implementation works, threat model that, and look at it from a broader picture.”
David Falgiano, CISSP, VP of Security Engineering at M&T Bank, and Rich Popson, Senior Information Security & Risk Manager (CISO) at Sensata Technologies dropped by to give us their lessons learned dealing with PKI challenges throughout their careers.

When asked about attracting and maintaining PKI talent, Rich said it’s not an easy task.
“I think what ends up happening is, once you start talking about encryption, eyes tend to glaze over, and people really don’t fully understand it,” said Rich. “So trying to get people who can fully understand what really PKI is, and just what security threats are actually out there, it’s very difficult to do. And it’s a never-ending learning process, and people are just not willing to step up, and just continue to learn.”
Dave shared his thoughts on how to speak the business about the importance of PKI and encryption practices.
“When you’re talking with the business, you want to be talking about it from two perspectives,” said David. “PKI is important, encryption is important. But be able to talk to them in risk terminology, how we’re taking your stuff, and trying to decrease the risk of a bad guy getting it. We can’t eliminate it, but we’re trying to decrease that risk.”
Certificate Management and Replacing Machine Identity Solutions
The use cases for certificate management and automation seem to never stop growing. From integrating with secrets with HashiCorp Vault to setting up autorenewal workflows with certificate stores, there’s a lot of things your teams can take advantage of to build tighter certificate security.
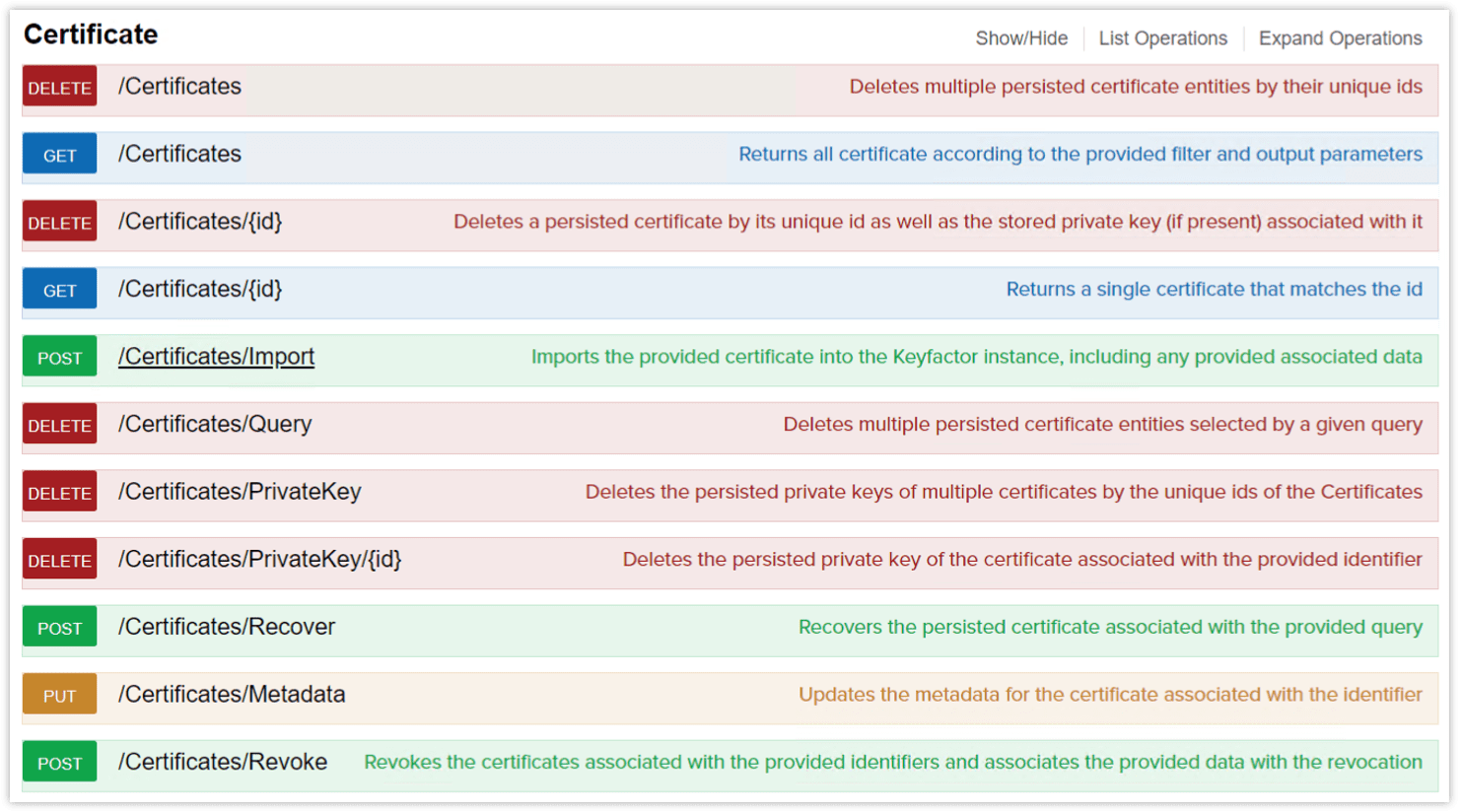
Rex Wheeler, Director of Integrations, showcased all the different ways to extend Keyfactor Command’s certificate automation capabilities by using:
- Gateways to connect with your Certificate Authorities
- Orchestrators to integrate with Certificate Stores
- Workflow handlers to trigger Lifecycle Alerts
- Swagger REST API to build customer integrations
- And more…
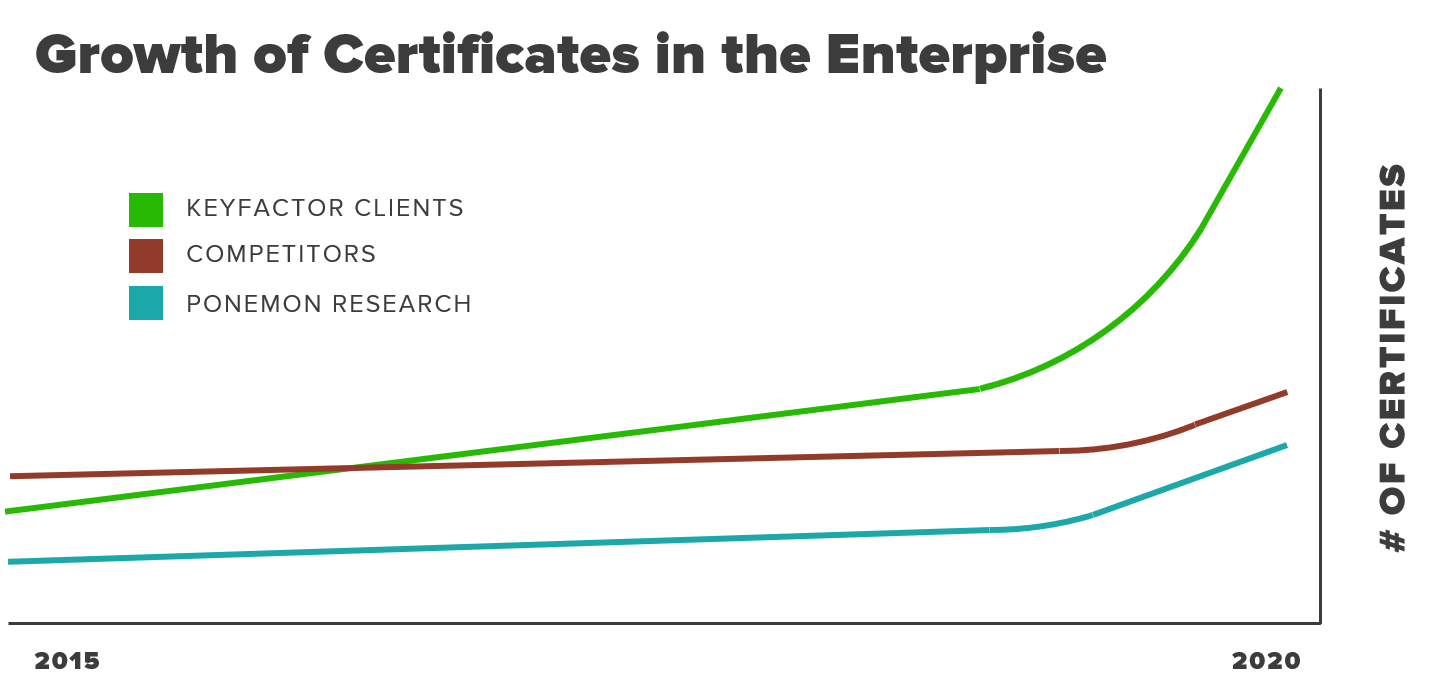
The need for better machine identity management solutions is real.
More than 20% of Keyfactor customers came to us after deploying legacy solutions. If you’re looking to replace a legacy certificate management solution or move your PKI to the cloud, these sessions were for you.
In my session with Niko Ruhe, we showed how you can up-level to Keyfactor and migrate from your legacy machine identity management platform.
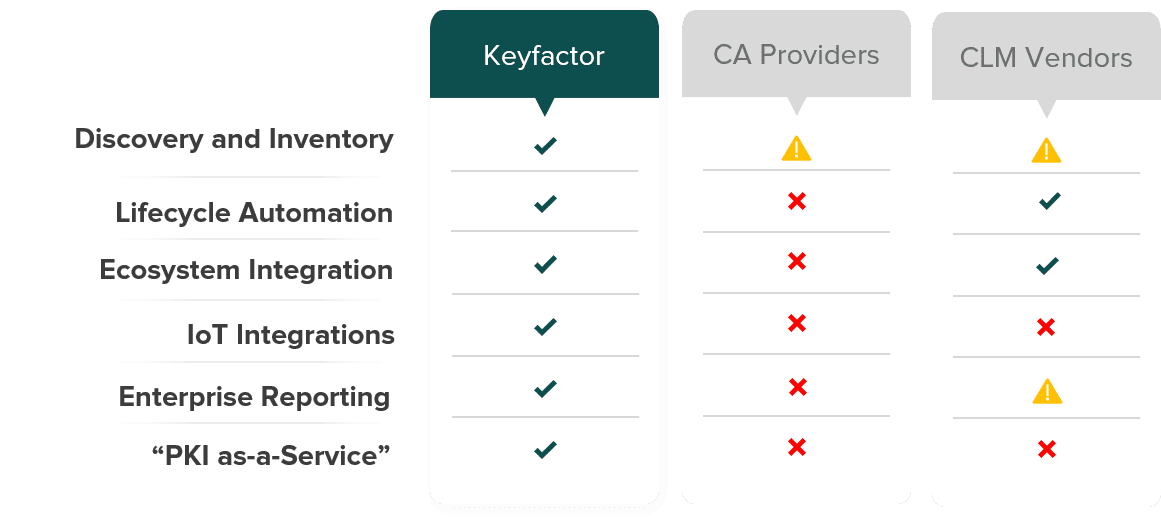
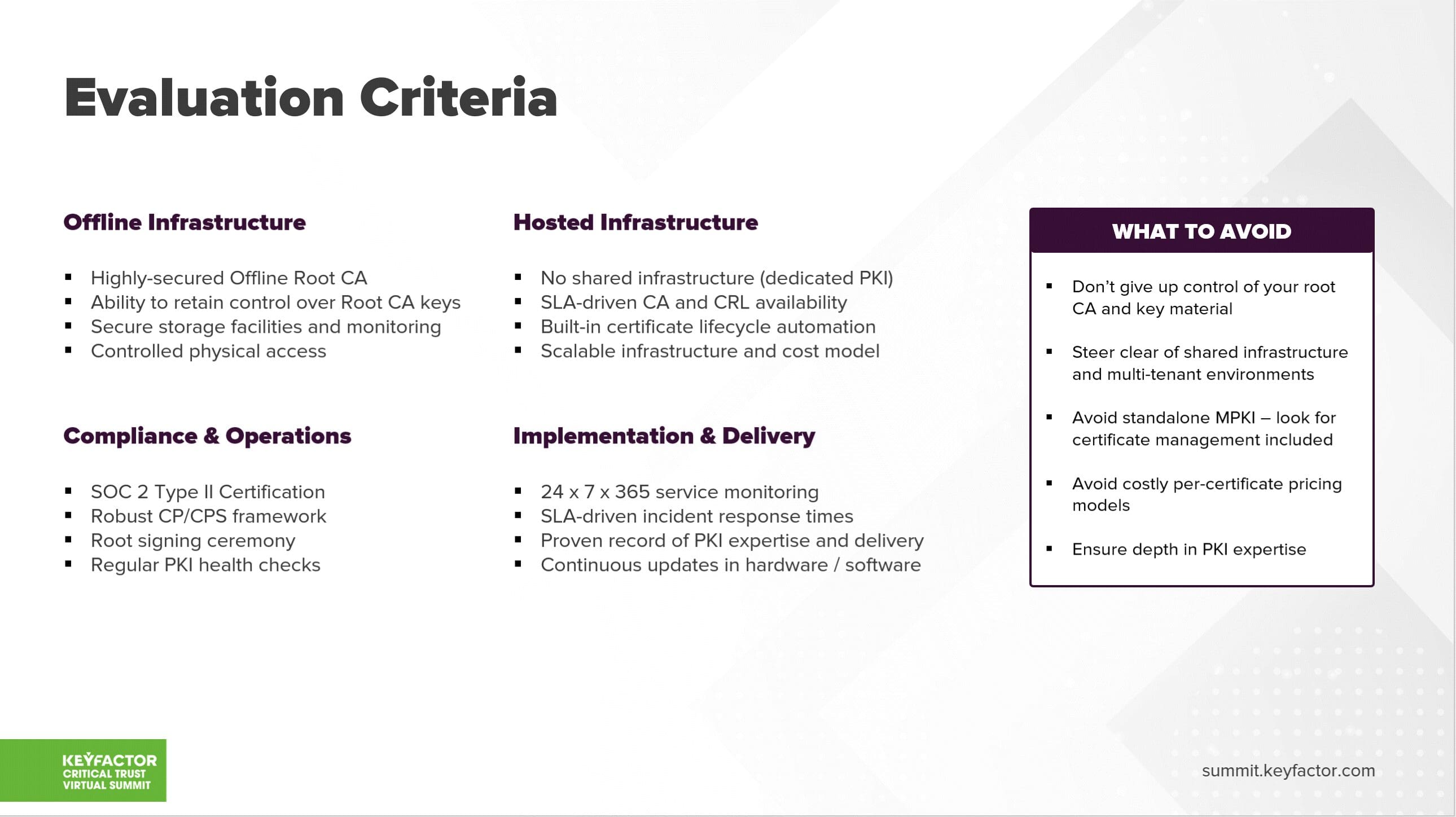
Toby and Kevin walked through the steps you can take to move your PKI to the cloud and break down evaluation criteria that should always be considered.
DevOps Inspiration from Netflix
It shouldn’t come as a shock that most attendees at this summit work in InfoSec and security.
At Keyfactor, we’re constantly being asked how security teams can shift-left in their security practices. Whether it’s integrating cryptography practices with popular DevOps tools or how these two teams can work better together, development and security teams will need better alignment to succeed in today’s multi-cloud world.
Well, what better way to understand the mind of a DevOps engineer than to have Andy Glover from Netflix.

In his session, Andy shows why he firmly believes that their success is in large part because they learn quickly and apply those lessons throughout the product in short order.
Andy walkthrough the principles that Netflix uses (and you can to!) to out-innovate their competition because of their continual investment in automation allows them to do so.