In its 2021 Top Security and Risk Trends for 2021, Gartner identified Cyber-savvy boards as a top priority for organizations, as the number of highly publicized security breaches continues to grow. In this blog, we break down why board members should pay closer attention to security posture and what it takes to establish a cyber-savvy board.
Cyber risks are business risks
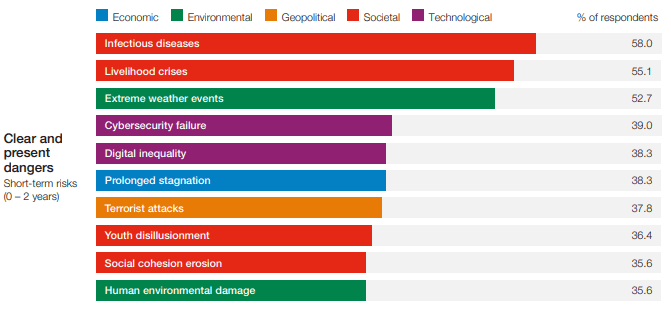
Every year, the World Economic Forum publishes the Global Risks Report, which identifies all risks that businesses face today – ranging from climate change, political and societal instability, to cybersecurity and health disease.
With businesses becoming increasingly digitized and dependent on cyber-enabled technologies, cybersecurity threats and data-related risks, and the risk management strategies to alleviate them, have become a top priority. In fact, the World Economic Forum 2021 Global Risks Report has ranked cybersecurity failure as one of the top five short-term business risks.
Cybersecurity threats and data-related risks, and the risk management strategies to alleviate them, have become a top priority for digitally transformed companies. There are a variety of factors causing an enterprise’s threat surface to expand faster than ever before:
- The ongoing migration to the cloud, which accelerated as a response to the pandemic.
- The widespread shift to remote work and the need to support work-from-anywhere initiatives where employees bring their own devices.
- Increased dependence on extensive and complex supply chains, leaving organizations vulnerable to risks inherited by third parties and partners.
- An extended patchwork of data privacy and protection regulations with requirements for data residency and encryption.
Cybersecurity is a shared responsibility
Criminals and adversaries are exploiting the evolving and expanding threat landscape to launch cyber-attacks which increase in number and sophistication. As cyber-attacks affect more and more the physical world, the consequences of these attacks are also escalating.
According to a Gartner report, by 2024, 75% of CEOs will be personally liable for cyber-physical security incidents, while by 2023, the financial impact of a cyber-physical attack resulting in fatalities is expected to reach over $1 billion dollars. Gartner states that “Even without taking the actual value of a human life into the equation, the costs for organizations in terms of compensation, litigation, insurance, regulatory fines and reputation loss will be significant.”
Considering the far-reaching effects of cyber-physical incidents and attacks, industry leaders must realize that cyber risks are as possible and impactful as the “traditional” risk they are used to confront. In fact, cyber threats can be the source of business risks if appropriate measures to prevent them are lacking. It is also important to understand that cyber risk is not the job of solely the IT department. An isolated approach to cybersecurity creates more blind spots that can be exploited by cybercriminals.
Siemens mentions in a report:
“Cybersecurity should be a shared responsibility of all employees in a company, from the executive suite to close collaboration among OT, operations, and enterprise IT. Cybersecurity should also engage health, safety, and environmental (HSE) teams, because of the potential HSE impacts of a severe security breach. HR must be involved, too, because all employees need to be aware, trained, and accountable for their potential roles, intentional or not, in opening the doors — physically or virtually — to attackers.”
Cyber-savvy boards for cyber-resiliency
It is no wonder that cybersecurity has become a top priority for the executive board. In the Gartner 2021 Board of Directors Survey, directors rated cybersecurity the second-highest source of risk for the enterprise after regulatory compliance.
Cybersecurity incidents represent potential business losses that must be treated with the same vigilance as more traditional vectors of business disruption and loss of profit. Additionally, in a connected digital world, an incident or breach at one department or one organization may ripple across supply chains and even industry sectors—and in some cases result in major structural damage to the nation.
Daniel Dobrygowski, head of Corporate Governance and Trust at World Economic Forum, said that “We need effective collaboration and strategic vision to ensure cyber resilience and protect trust between all stakeholders.” Changes in the industrial threat landscape make necessary an increased emphasis on cybersecurity as a strategic, enterprise-wide risk.
As a result, Gartner has identified in the Top Security and Risk Trends for 2021 report the shift towards creating cyber-savvy boards. To do so, businesses are creating a dedicated committee that focus on discussing cybersecurity issues. This committee is often led by a board member with security experience or a third-party consultant. In fact, Gartner predicts that by 2025, 40% of boards of directors will have a dedicated cybersecurity committee overseen by a qualified board member, up from less than 10% today.
The shift towards cyber-savvy boards will signal two things:
- Increased support – budget and resources – to address the threat landscape.
- Increased scrutiny and expectations from the CISO and the security teams to meet the requirements set by the Board to protect the organization against cyber-attacks while ensuring business continuity.
A cyber-savvy board can motivate the whole chain within an organization to view cybersecurity as everyone’s responsibility – they provide a vision for everyone to follow. This vision should be based on the following pillars:
- Cybersecurity strategy. A strategic vision and a tactical, operational plan to move along can proactively protect corporate assets and adapt to the emerging cyber threats and evolving regulatory requirements.
- Policy review. Corporate cybersecurity policies and practices, as well as roles and responsibilities, should be evaluated to ensure they are current and adequate to protect the organization. Together with policy review, the board should revisit the budget allocated for cybersecurity and privacy to ensure these initiatives are properly funded.
- Lead by example. Cybersecurity policies must be enforced and supported by the company’s leadership who should have the capacity to communicate an enterprise-wide plan to manage cyber risk, engaging all employees.
- Business continuity. The board should oversee the development of a comprehensive incident response plan that will ensure business resilience and continuity even during a cyber-attack. The plan should be widely understood and drilled.
- Continuous monitoring and assessment. The board should periodically monitor and revise the organization’s cybersecurity controls and capabilities, adjusting to new vulnerabilities and external threats.
- Cybersecurity awareness. The board should ensure that the company implements a comprehensive cybersecurity education program to foster a culture where all employees embrace responsibility for cybersecurity.
With cyber-attacks no longer being a question of “if”, rather a matter of “when and how often”, cybersecurity should not be an afterthought. Instead, it should be woven into the organization’s fabric to ensure that critical assets, brand reputation, and regulatory compliance are not jeopardized. It is time that all organizations transformed their boards into cyber-savvy ones to promote resilience and business continuity.
Cybersecurity and machine identities
Machine identities – cryptographic keys, digital certificates, and secrets – underpin identity and trust in cybersecurity today. However, the importance of machine identities is often overlooked by IT and security leaders that, in many cases, aren’t aware of the full scope and associated risk of unknown or unmanaged machine identities in their organization.
According to Gartner, machine identity management is now imperative. That’s why we put together the first-ever report on The State of Machine Identity Management with responses from over 1,100+ IT and security professionals. Get the full report below.

