Would it be surprising to know that over 74% of organizations don’t even know how many keys and certificates they have, much less, where they are or when they expire? A recent industry report highlighted this eye-opening statistic along the reality that massive scale of public/private keys and certificates needed to keep enterprises secure has created a Critical Trust Gap.
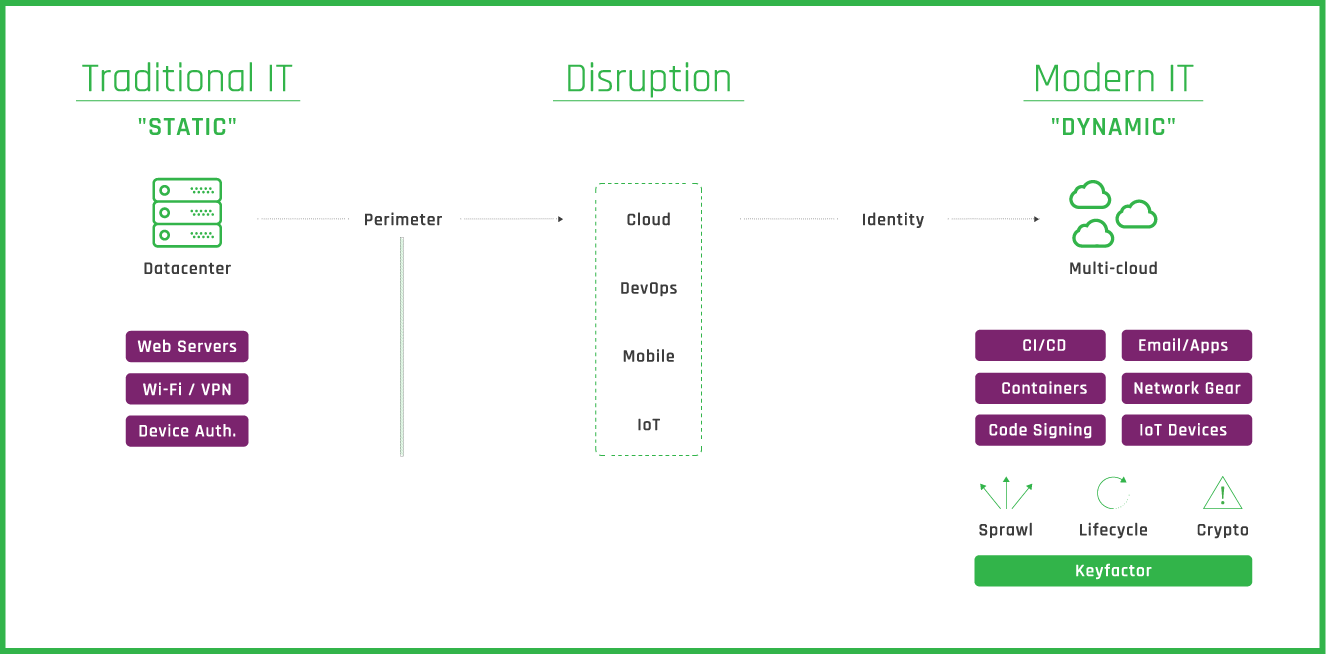
Before we get to understanding how to identify this gap, it’s important to understand how enterprise infrastructure has changed over time.
Traditional IT -- High Trust Infrastructure and Securing the Perimeter
In traditional IT from 10 to 15 years ago, most of your data and applications ran on dedicated infrastructure inside your data center. These servers were manually configured by IT and operations teams to run for long periods of time. This static approach was also copied for the security team by primarily focused on configuring the inside perimeter. The perimeter contained defenses that defined what came inside the organization, and what connections were permitted outside the perimeter.
Public Key Infrastructure (PKI) in this environment primarily focused on SSL/TLS certificates used to secure internet facing assets (e.g. web transactions, websites). These First Gen PKI or web PKI operations were limited in scope and required minimal overhead. Security may only need to manage 100 certificates or less, so they could get away with managing these certificates on a spreadsheet.
However, as the enterprise network grew, there was a need to stand up private PKI to manage communications and data. This required them to configure certificate authority (CA) software and start issuing certificates for Wi-Fi, VPN, and device authentication. Most of these certificates were automated through auto-enrollment. While this may have worked to help secure their internal assets, a new age of disruption has made managing private PKI extremely complex.
Disruption to Enterprise Networks
The Internet has become the new operating platform and traditional on-premises security models are no longer effective on their own. This should be no surprise to everyone, but it’s important to understand what factors cause this disruption to enterprise networks.
- Adoption of the Cloud: CIOs still list cloud as one of their top priorities for 2020. Moving to a native cloud environment drastically differs from your once highly secure, trusted network you’ve been protecting.
- Acceleration of DevOps: As developer and operations teams seek to deploy weekly, daily, and even hourly, they leverage cloud infrastructure to orchestrate their delivery faster than ever before. Faster deployments lead to higher risk of data exposures and corporate security gaps.
- Increased Workforce Mobility: It’s rare in today’s world to not have a work from home policy. We’re able to now complete most of our work from home, a coffee shop, or even on the beach. Whether it’s a mobile phone, laptop, or tablet, all these devices connect through internet to your enterprise network for email access and running business critical applications (e.g. ERP).
- Explosion of IoT: Gartner recently forecasted that enterprise and automotive Internet of Things (IoT) market will grow to 5.8 billion endpoints in 2020. Keeping track of authenticating and controlling access to billions of IoT devices seems insurmountable.
Modern IT -- Low Trust Multi-Cloud and Securing the Data
All this disruption has forced companies to adopt a multi-cloud strategy for infrastructure. This new strategy has shifted focus from securing the perimeter, to securing the data and applications themselves. We do this by using public/private keys and certificates – known as digital identities.
The expansive use cases now available for using PKI have grown at the same rate of the digital identities that you need to protect. Instead of managing a few hundred certificates, security operations now need to manage thousands to millions that operate within multi-cloud infrastructure.
Here are just a few use cases for PKI in multi-cloud infrastructure, and some implications to consider:
- Using Containers: DevOps teams use highly automated containers (e.g. Kubernetes, Docker) as their building blocks for delivery software in cloud environments. However, if containers are being spun up and torn down through automation, can certificates be securely and reliably provisioned to containers at the same rapid-fire speed?
- Embracing CI/CD: Continuous delivery (CD) pipelines allow teams to use continuous integration (CI) tools like Jenkins to build, test, and deploy their code. These teams tend to operate in silos outside traditional PKI governance through a self-signed CA (e.g. HashiCorp Vault). While teams release faster, security is unaware of increases in the untrusted and unknown number of certificates.
- Secure Code Signing Operations: The speed and scale of code signing has also increased with a diverse workforce around the globe. Most enterprises have a mix of both full-time development and services providers that need to sign code without exposing private keys to potential attack.
- Scaling Mobile Devices and IoT: Enterprise mobility management tools also use certificates to secure mobile devices outside the traditional use of PKI. When you add in the explosion of IoT devices which need authorization and unique identities, the problem of scale continues to grow.
- Accessing Distributed Network: Before, we could trust nearly everything inside our network environment protected by the perimeter. Now routers, switches, load balancers, and firewall appliances all need a unique identity to be trusted.
These use cases highlight new complexities in managing the lifecycle of digital identities at scale. Mismanaged private/public keys and certificates continue to disrupt operations and undermine trust in many organizations today, resulting in a Critical Trust Gap
The bottom line: the Critical Trust Gap must be identified, recognized, and closed to ensure corporate security.
How to Identify a Critical Trust Gap
These use cases convey good news for those looking to leverage PKI more broadly in their organization. However, it’s bad news if their PKI has not been built for this level of scale and complexity.
Here are some of the key indicators from our recent industry report that identify a Critical Trust Gap:
- Operational Outages: Over the past two years, 87% of respondent’s experiences unplanned outages due to expired certificates and 55% experienced four or more. Considering that Gartner estimates that one hour of network down time equals $300,000, it’s not hard to see exactly how costly operational outages effect the business.
- Failed Audits: Beyond operational outages, respondents also admitted that they’ve experienced an average of 6 failed audits in the last two years that posed a serious security risk.
- Staff Shortages: PKI expertise is a rare skillset to find and placing talent within your organization proves challenging for most. This leads to a lack of control over the internal processes needed to issue, deploy, and manage digital identities throughout their lifecycle. Only 38% of respondents believed that had acceptable PKI coverage on staff.
- Lack of visibility/control: As we’ve already mentioned, 74% of companies don’t know the exact number of keys and certificates their organization has dispersed across a mix of multi-cloud, mobile and IoT platforms. Furthermore, over 76% of respondents indicated that failure to secure these keys and certificates undermines the trust in their business.
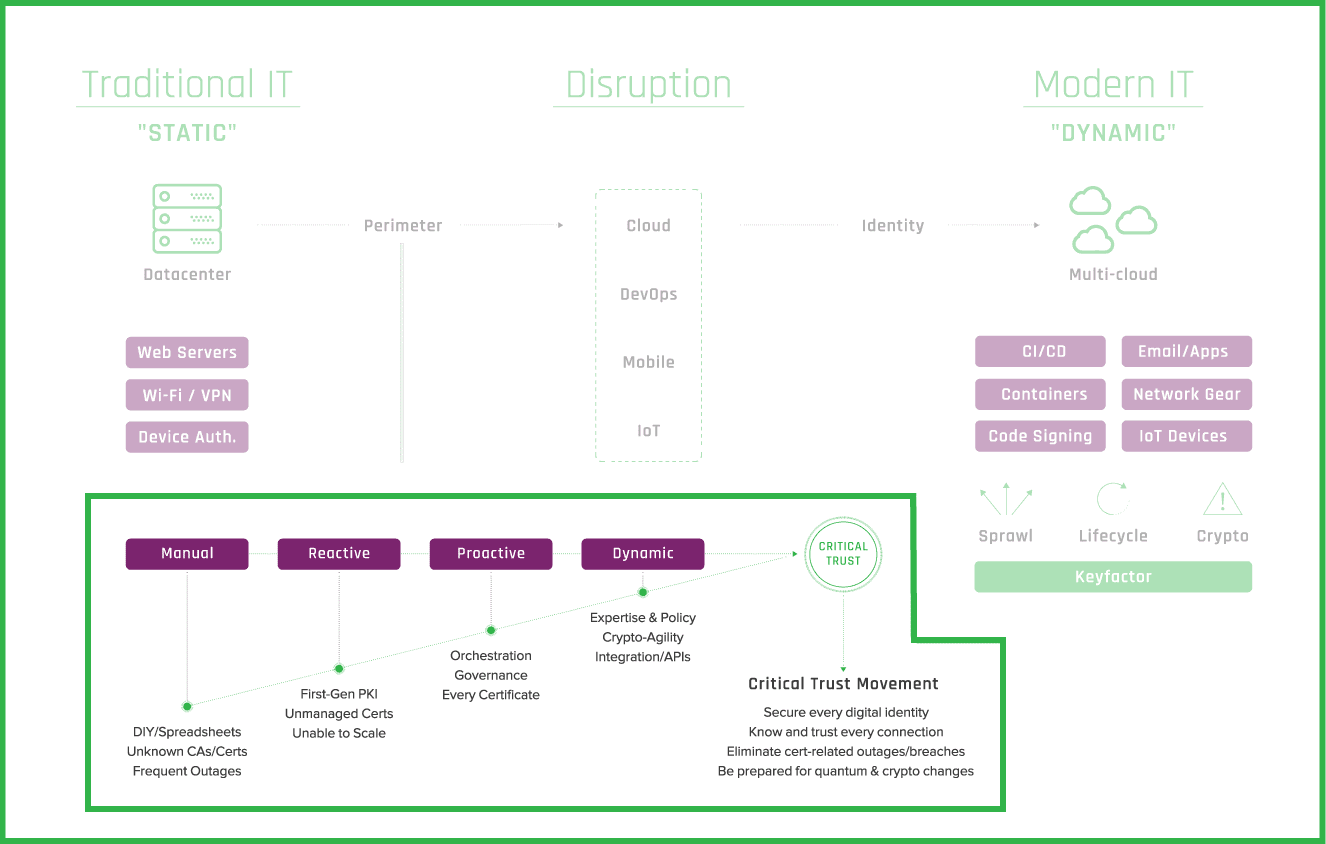
Closing the Gap
Without properly assessing how your organization currently manages keys and digital certificates, the Critical Trust Gap will only get larger as your organization continues to grow in the number of digital identities it depends on.
Here are some helpful ways to consider closing the Critical Trust Gap.
- Re-think Your PKI: The reality of PKI use cases can be overwhelming and it’s imperative you have a long-term strategy for managing your PKI. Conduct an audit to find who “owns” PKI in your organization and how they manage it amongst their other responsibilities. Track how many digital identities your organization issues week over week to see where maximum capacity could reach a break point.
- Move from being Reactive to Proactive: According to Gartner*,“Security leaders that successfully reposition X.509 certificate management to a compelling business story, such as digital business and trust enablement, will increase program success by 60%, up from less than 10% today.” You need to level-up the conversation from viewing secure identities as a hassle to a core component of securing your digital business.
- Plan Ahead for Crypto-agility: Most organizations have planned for advancements in quantum computing and how it will effect encryption practices. However, almost 50% of respondents are concerned that the rise of quantum will require significant changes to PKI and certificate management practices. Solving for the future of quantum computing needs action now, not during its eventual arrival.
*“Technology Insight for X.509 Certificate Management”, David Mahdi, David Collinson, October 2019


