In December of 2011, the CA/Browser Forum, comprised of representatives from the major Certification Authorities such as Symantec, Comodo, GoDaddy, and DigiCert, as well as browser vendors such as Microsoft, Apple, Mozilla, and Opera, published a document called “Baseline Requirements for the Issuance and Management of Publicly Trusted Certificates.” This document outlines an agreed-upon set of minimum standards for SSL/TLS cert vendors.
One of these standards essentially calls of the elimination of certificates with 1024-bit RSA public keys by the end of 2013: any RSA-keyed certificate, even end-entity (“subscriber”) certificates, that expire after Dec. 31, 2013, must have a key of at least 2048-bits. This is big news in some circles; a number of public cert vendors have had to change their procedures, and, more significantly, start migrating their customer bases to 2048-bit certs. Many started this process quite a while ago.
But this has also caused some concern amongst organizations that operate their own internal PKI… last fall, Microsoft issued an update that invalidated any cert with an RSA key of 512 bits or less… is a similar measure coming for 1024-bit certs?
In many cases, these organizations are unable to get rid of smaller key sizes, due to limitations of legacy hardware that their PKI must support. As PKI implementers, the Certified Security Solutions (CSS) PKI team frequently has to back away from our preferred algorithm choices due to these sorts of limitations. While it is extremely important for organizations to have a migration plan to move away from 1024-bit certs in their environment, an across-the-board blockade of 1024-bit certs today would be catastrophic in many cases.
So far, I think we’re safe. The CA/Browser forum makes it pretty clear that their guidelines are for publicly-trusted CAs only. From the opening paragraphs: “These Requirements do not address the issuance, or management of Certificates by enterprises that operate their own Public Key Infrastructure for internal purposes only, and for which the Root Certificate is not distributed by any Application Software Supplier.” I’ve asked around various Microsoft contacts, and have heard of no plans for an outright block of 1024-bit certs…yet.
Of course, it’s still a very good idea to start migrating 1024 bit certs out of the environment as best you can. If you have a Microsoft-based PKI (AD CS), and it’s used heavily, there’s a good chance you have some, since many of the default Microsoft cert templates have a minimum key size of 1024.
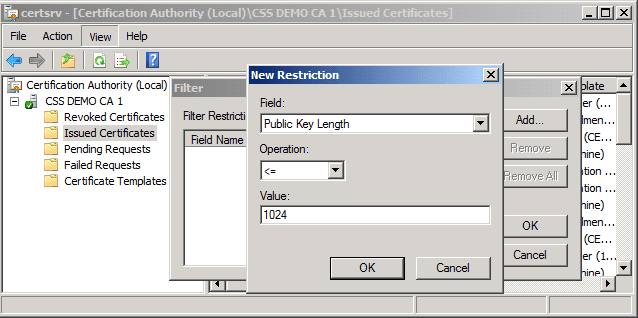
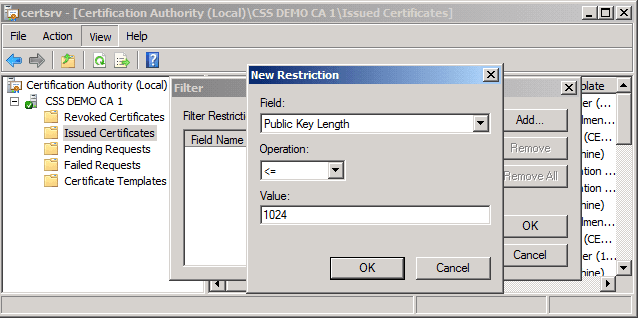
Simply getting an inventory of the 1024-bit certs you’re using is a good start. You can do this from within the Certification Authority management console, using a filter (“View->Filter…” from within the mmc). The example below shows how to display only the certificates with key sizes of 1024 bits or less:
Once you have an inventory, you can start making a determination of what your 1024-bit certificates are being used for, and what machines or devices they’re being delivered to. If the systems in question support RSA 2048, migration should be relatively easy. If not, more migration planning may be required. However, reducing the scope of the issue to the bare minimum should make it easier to develop workarounds, if and when a 1024-bit “blockade” becomes a reality.